The Vocabulary Shift That Changed the Rules
Something happened to the word “security” over the past decade, and the consequences are still playing out. It used to have a reasonably clear meaning. Security was about borders, armies, intelligence agencies, and the physical protection of states and citizens — a domain with defined edges. Trade policy was trade policy. Industrial policy was industrial policy. Infrastructure investment was infrastructure investment. They were separate categories with separate bureaucracies, separate legal frameworks, and separate political constituencies.
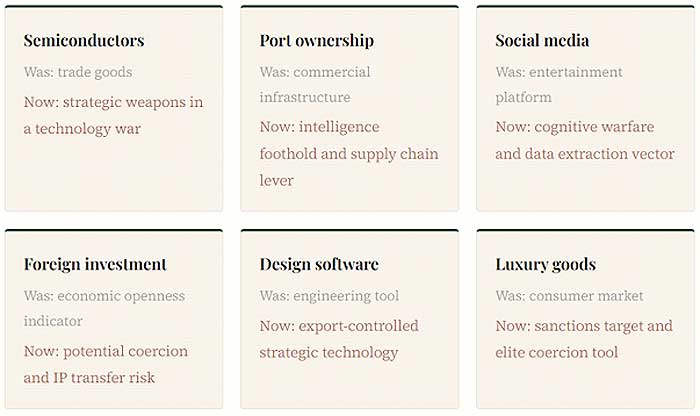
That separation is gone. A semiconductor is now a weapon. A port is a strategic vulnerability. A social media app is an intelligence operation. A foreign purchase of a domestic power plant is an act of potential coercion. The vocabulary of national security has colonized virtually every domain of public policy, and the colonization has happened so fast and with so little friction that most people have not stopped to ask what it means when everything qualifies.
This is not entirely cynical. Some of the threats are real. The interdependencies are genuine. The idea that a liberal open economy could simply ignore what adversaries were doing inside its critical infrastructure turned out to be dangerously naive. But the securitization trend has also become its own political logic, one that justifies almost any intervention, forecloses almost any trade-off, and generates almost no accountability because security threats are by definition too sensitive to subject to normal democratic scrutiny.
How We Got Here
The intellectual groundwork was laid before the current moment, but it was China’s rise and the 2008 financial crisis that gave it political traction. The crisis demonstrated that economic interdependence could be a vulnerability as much as a strength. China’s accession to the WTO and the subsequent hollowing out of Western manufacturing provided the political energy. Russia’s annexation of Crimea in 2014 added the coercion dimension: here was a state using energy dependence as a geopolitical weapon in real time, against European allies, and Europe had no immediate response.
Export controls traditionally had narrow economic effects. But the expansion of chip controls on China had sweeping commercial impacts, partly because of China’s military-civil fusion strategy, which deliberately broke down barriers between the civilian commercial technology sector and the defense industrial base. When a state’s civilian and military technology ecosystems are fused by design, it becomes genuinely difficult to separate economic competition from security concerns. Both sides, in different ways, had built a system that made the distinction almost impossible to maintain.
Over time, US allies grew skeptical of America’s national security rationale for export controls targeting China’s semiconductor industry. The question being asked, quietly, was whether these actions were rooted in genuine security concerns or in commercial competition dressed up as security. That skepticism is telling. It points to the central tension in the securitization trend: once you frame competition as security, you lose the ability to distinguish between protecting genuinely vital interests and protecting incumbents. The policy tools for each purpose are very different. The costs are not comparable.
Case Study One: The Chip War and Its Discontents
The US-China semiconductor confrontation is the defining case of economic securitization, both because of its scale and because of how visibly the logic keeps colliding with its own contradictions.
In 2025, the contest moved from tariff skirmishes to a confrontation over strategic choke points. Washington expanded semiconductor export controls, limiting China’s access to advanced chips, design software, and lithography tools. The Trump administration tightened these rules in September, extending them to foreign affiliates. Beijing retaliated ten days later with new licensing requirements on rare-earth oxides, metals, and magnet products. The escalation jolted global markets and forced emergency consultations in South Korea, where both sides agreed to a tentative one-year suspension.
The EDA software ban illustrates the pattern at its most acute. In May 2025, the US restricted exports of chip design tools to China. Within weeks, China retaliated with rare earth restrictions. By late June, a deal was struck that saw the US lift EDA restrictions while China agreed to expedite rare earth shipments. Despite lasting just a few weeks, the damage had been done: Chinese design teams faced delays, some were forced to revert to outdated toolsets, and trust across the supply chain had been further eroded. A ban introduced on security grounds, reversed on economic grounds, in under two months.
“The chip war has not isolated China from advanced technology. It has given China the most compelling possible reason to build its own, and the political cover to mobilize the resources to do it.”
China’s 15th Five-Year Plan, adopted in early 2026, reveals that Beijing has shifted its measurement of success. The 70% semiconductor self-sufficiency target from Made in China 2025, a target China missed by roughly 50 percentage points, has been quietly deleted and replaced with a deployment metric: digital economy value-added at 12.5% of GDP by 2030. Beijing is no longer measuring success by how many chips it produces. It is measuring success by how deeply computing infrastructure penetrates the economy. The controls intended to contain China’s technological ambitions have redirected them into something considerably harder to target with export controls. A Peking University research team in March 2025 announced a 2D transistor material that could operate 40% faster than TSMC’s 3-nanometer devices while consuming 10% less energy. The pressure works. Not in the direction Washington intended.
Case Study Two: Europe Builds a Fortress, Unevenly
European foreign investment screening is the quieter but structurally more consequential securitization story. For most of the 2010s, Europe’s approach to Chinese investment was, charitably, permissive. Between 2000 and 2023, China’s state banks and official creditors channelled around €138 billion into EU economies. From 2015 to 2018, Chinese buyers acquired a string of strategic semiconductor assets with an 80% completion rate on attempted acquisitions, spanning intellectual property, tools, wafers, foundries, and power chips. At the time, political scrutiny in Europe was minimal and coordination across member states virtually non-existent.
The reckoning came late. Following a wave of takeovers of semiconductor companies including Silex, Okmetic, LFoundry, and Nexperia, member states strengthened screening mechanisms. Large member states and the UK have since blocked or unwound numerous Chinese acquisitions, particularly after Beijing supported Russia’s invasion of Ukraine. On February 10, 2026, the EU released an agreed compromise text of a new Foreign Investment Regulation, mandating screening mechanisms across all member states and closing the EU-subsidiary loophole that had allowed Chinese investors to enter through lighter-touch jurisdictions.
The problem is consistency. Bulgaria, Greece, and Ireland only introduced screening mechanisms in 2025. Croatia and Cyprus are still finalizing theirs. Chinese FDI has meanwhile shifted from mergers and acquisitions toward greenfield projects in automotive and battery sectors, directed toward more accommodating member states such as Hungary. The fortress has walls, but several gates remain open, and sophisticated investors have no trouble finding them.
The deeper issue is that Europe’s screening apparatus functions partly as industrial policy under security cover. France’s blocking of the Couche-Tard bid for Carrefour — a Canadian firm buying a French supermarket chain — had nothing to do with espionage. It had everything to do with economic nationalism. Once the securitization vocabulary is available, it gets used for purposes far beyond the original mandate. Every government that acquires the legal tools of security review acquires the incentive to deploy them opportunistically.
Case Study Three: TikTok and the Algorithm as Geopolitical Object
TikTok is probably the most legible illustration of securitization at the level of popular culture, because the object being securitized is something hundreds of millions of people use to watch short videos on their phones.
In January 2025, the US Supreme Court ruled in favor of a law banning TikTok unless ByteDance sold its US assets, citing national security concerns and data collection practices. TikTok’s servers went dark for several hours before being brought back online through an executive order from President Trump. By December 2025, ByteDance had signed a deal to divest a portion of US assets to a consortium including Oracle, private equity firm Silver Lake, and an Emirati-backed investment firm. In July 2025, European regulators announced a €530 million fine against TikTok for unlawfully transferring European data to China in violation of GDPR — this despite EU regulators having been noticeably slower to act against TikTok than against American platforms.
What TikTok represents is the securitization of attention. The argument is not merely that the platform harvests data, though it does. It is that the algorithm, the system that decides what you see is a potential vector of influence, and if that algorithm is ultimately subject to Chinese government direction, then hundreds of millions of Western users are potential subjects of a foreign cognitive operation. That argument may well be correct. It is also, structurally, an argument that could be made about almost any large platform with foreign ownership or foreign infrastructure dependencies. The TikTok precedent does not create a narrow exception for Chinese social media. It establishes that algorithm curation is a national security matter. From there, the expansion is limited only by political will.
Case Study Four: The Port as Threat
Port ownership seems, on the face of it, an unlikely candidate for securitization. Ports move containers. The securitization argument runs: whoever owns the port controls the data flowing through it, can monitor shipping patterns, identify military logistics, throttle supply chains in a crisis, and provide a physical foothold for intelligence operations. China’s COSCO and its subsidiaries hold significant stakes in European ports including Hamburg, Piraeus, Antwerp, and Valencia. The Czech government in March 2025 formally halted a Chinese investment in a strategic sector, marking its first formal veto under its updated screening framework, citing espionage risks.
Each step in the chain follows logically from the previous one. Each step also captures more of the economy within the security review framework, giving the state more latitude to intervene on grounds that cannot be publicly scrutinized without compromising the intelligence assessments that supposedly justify the intervention. There is no agreed principle for where the perimeter stops. And in the absence of such a principle, it does not stop.

When Everything Is a Threat, What Is Security?
The securitization trend has no natural stopping point. Security has always been expansionary: every security bureaucracy expands its mandate over time, because the downside of missing a threat is catastrophic and the upside of excessive caution is invisible. Add geopolitical competition, supply chain fragility, digital interdependence, and a political environment in which “national security” is one of the few bipartisan concepts remaining in Western democracies, and you have a concept that can absorb almost anything. The export controls imposed on Russia following the Ukraine invasion targeted not only factories producing weapons but also luxury goods from brands including Gucci and Versace. The rationale: imposing economic pain on elites. Luxury handbags as security policy.
Three consequences of this deserve attention.
1. The erosion of rules-based trade architecture. The WTO has security exceptions, but they were designed to be narrow and rarely invoked. They are now invoked routinely by major economies for measures primarily about industrial competition. The December 2025 USTR determination that China’s semiconductor strategy poses a direct threat to US commerce set a tariff at 0% initially, rising in 2027, intended as much to retain leverage as to deliver immediate economic impact. Tariffs as signals. Tariffs as threats. The WTO was not designed for this and has no effective response.
2. The democratization problem. Security policy has historically operated outside normal democratic accountability. When security logic extends into trade, investment, technology, and infrastructure, those same accountability limitations follow. Decisions with enormous economic consequences can be justified by classified assessments that affected parties cannot see, challenge, or rebut. The legal frameworks are catching up. The political incentives all run toward more classification, not less.
3. Blowback. Every security intervention in the economic domain teaches the target to develop alternatives and reduce dependency. China’s semiconductor self-sufficiency drive was not made more likely by export controls. It was made certain by them. The controls intended to preserve Western technology leadership may be accelerating the development of competing ecosystems that do not depend on Western supply chains at all. Beijing’s 15th Five-Year Plan has quietly shifted from production targets to deployment targets, which are considerably harder to constrain.
The Concept Under Strain
The word “security” is doing too much work. It is being asked to justify industrial policy, protect incumbents, manage geopolitical competition, regulate information ecosystems, and provide political cover for measures that would not survive scrutiny under their true rationale. The more it is stretched, the less it means, and the more it becomes a label that governments apply to whatever they want to do without having to justify it in ordinary policy terms.
None of this means the underlying concerns are fabricated. Supply chain dependencies are real vulnerabilities. Data harvesting at scale is a genuine risk. The concentration of critical infrastructure in the hands of geopolitical rivals raises legitimate questions. The securitization trend did not emerge from nothing. It emerged from real failures to take seriously the ways in which economic openness was being exploited, sometimes deliberately and systematically. The 2010s European garage sale of semiconductor assets to Chinese buyers, conducted with minimal scrutiny, was a genuine lapse that has had lasting consequences.
But a concept that means everything means nothing. If security justifies blocking a supermarket acquisition, restricting a design software license, forcing a social media sale, and reviewing a port investment all under the same analytical framework, then it has stopped being a framework and become a political convenience. The countries that navigate the next decade most effectively will be those that develop a more disciplined account of what actually constitutes a security threat, rather than expanding the definition until it covers the entire economy. That work is harder and less immediately rewarding than invoking the word. It is also the only way to avoid building a security apparatus that cannot distinguish between protecting citizens and protecting incumbents — and eventually stops being able to tell the difference itself.


