The piracy and armed robbery (PAR) situation in the Straits of Malacca and Singapore (SOMS) was reportedly under control from 2017 to 2018. The Regional Cooperation Agreement on Combating Piracy and Armed Robbery against Ships in Asia (ReCAAP) Information Sharing Centre (ISC) recorded eight cases in 2018 compared to nine cases in 2017.[i] ReCAAP ISC attributed the improvement to the counter-piracy measures by the shipping industry and law enforcement agencies. Similarly, the International Maritime Bureau (IMB), in its 2018 annual report, cited the same measures to explain the improvement in SOMS.
However, recent cases suggest that the PAR situation in SOMS, especially along the Singapore Strait, is not under control. ReCAAP in January 2020 reported that there is a significant increase in cases since October 2019.[ii] From January to May 2021, the 15 cases that occurred along the Singapore Strait accounted more than 50% of cases in Asia (28 cases).[iii] In July 2021, the IMB highlighted the Singapore Strait as an area of concern.[iv] The perpetrators remain at large, and there are concerns that the prolonged COVID-19 pandemic affects economies of coastal communities, hence creating conditions for PAR to thrive.[v]
Figure 1: Map of the Straits of Malacca and Singapore
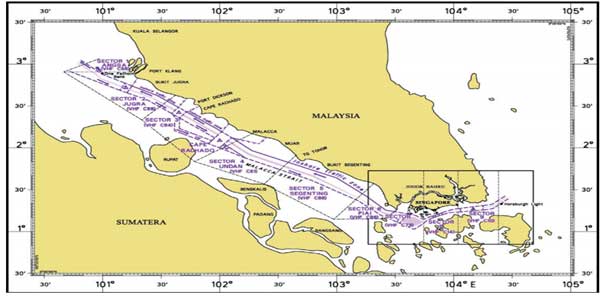
Source: Maritime Port Authority of Singapore
Why is PAR a persistent problem in SOMS? This paper examines the issue by providing a historical appreciation of SOMS and interrogating why the notion of “control” is problematic. It implies causation between counter-piracy measures and the underlying structural causes of PAR. Instead, the problem waxes and wane as a function of counter-piracy measures on the one hand and pull and push factors of the PAR business on the other hand.
A WATERWAY OF GLOBAL IMPORTANCE
SOMS is a crucial waterway in Southeast Asia (SEA) that serves as a “global shipping superhighway” and accounts for “a third of the world’s marine commerce.”[vi] The 16th-century Portuguese voyager Tome Pines recorded the historical importance of SOMS to global trade during the early age of European colonialism in his book “The Suma Oriental.” He wrote that “whoever is lord of Malacca has his hand on the throat of Venice.” In modern times, former Chinese president Hu Jintao in 2003 recognised the strategic importance of SOMS – “Malacca Dilemma” – to the economic growth of China.[vii]
Figure 2: Map illustrates a higher level of maritime activities in SOM vis-à-vis SEA

Source: live map from www.marinetraffice.com
PAR in SOMS is a maritime security concern for Singapore, given its plans to boost its economy. Singapore’s Tuas Mega Port is scheduled to be ready in 2040. Furthermore, a bustling maritime zone could inadvertently make SOMS a target-rich environment.[viii] An increase in shipping activities could create more opportunities for PAR.[ix] PAR in SOMS is also a concern to the Iskandar Development Region in Southern Johor, Malaysia, where the Port of Tanjung Pelepas and Johor Port are central to the region’s expansion. For the Riau Islands, Indonesia, shipping is crucial to the province’s free trade zone (FTZ).
PAR is SOMS could have wider implications for the region. The possible nexus between sea piracy and maritime terrorism is one of the primary maritime security issues for Singapore and other littoral states in Southeast Asia. The former President of Singapore, Dr Tony Tan Keng Yam, mentioned this point during his speech in 2004 when he was the Deputy Prime Minister and Coordinating Minister for Security and Defence.[x]
Figure 3: Map illustrates the high level of maritime activities in the Singapore Strait and near the Riau Islands province in which Batam is a known pirate hotspot

Source: live map from www.marinetraffice.com
HISTORY INDICATES ENDURING UNDERLYING CAUSES
Historical records show that PAR has been a maritime security problem in SOMS since the 14th century when seaborne trade increased. Given the situation, the Ming Dynasty despatched the famous Admiral Zheng He to battle the pirates.[xi] The historical trend up to the mid-2000s in which coastal states had to implement a raft of counter-piracy measures such as the Malacca Straits Patrol (MSP) indicates that PAR in SOMS is endemic.
Most of the cases in SOMS from 2017 to 2018 occurred along the Singapore Strait, and this pattern continues into 2021.[xii] From January to April 2021, the 12 cases that happened along the Singapore Strait accounted for 50% of cases in Asia.[xiii] These cases correspond to the geographical trend over the past decade. Pirates have been shifting more activities from the Malacca Strait to the Singapore Strait and nearby South China Sea (SCS) instead of relinquishing a life of crime.[xiv]
PAR activities could shift to areas, which the pirates perceive as having lesser counter-piracy patrols. Whenever cases were low, it is possible that pirate activities were still ongoing but below a certain threshold of violence and economic loss. This strategy could help pirates circumvent counter-piracy measures. Anthropological factors such as the “generational shift among the pirates” and the state of the relationship between pirates and criminal syndicates may also partially explain the geographical shift in PAR activities.[xv]
In sum, PAR is “immensely adaptive to changing situations”, and any “control” that counter-piracy measures have is temporary in the long run.[xvi] Conventional security/naval measures in counter-piracy have more impact on the symptoms or tactical aspects than the underlying structural causes that make PAR endemic.
LIMITATIONS OF CASE STATISTICS
Statistics are often used to demonstrate whether the PAR situation is under control or not, but this method has its limitations. Cases may either be over-reported or under-reported.[xvii]
Cases may be under-reported among the shipping communities because the victims are concerned that investigations could disrupt the ship’s schedule and commercial reputation, raising insurance premiums. Victims may not be overly worried if the economic loss is low, and the business could absorb it. The crew are generally unharmed as the pirates used minimal violence to avoid the attention of maritime security agencies. Some victims may not report cases to avoid the attention of governments if their ships are involved in unlawful activities. The activities include forced labour, smuggling, illegal, unreported and unregulated (IUU) fishing.
Victims from coastal communities who operate small fishing and trading boats may not report cases if they distrust local authorities. Some local authorities could be complicit in PAR activities or lack enforcement capabilities. Also, they fear retaliation as the pirates may come from nearby communities or the same islands such as Riau and have links to criminal groups on land. According to the IMB, statistics rarely capture cases involving fishing boats.[xviii] Therefore, while official statistics may paint the picture that the PAR situation is under control, the reality on the ground may be different.
Cases may also be over-reported due to possible insurance fraud or victims reporting more petty thefts and failed PAR attempts.[xix] These cases could have gone unreported in the past to avoid the hassle of making reports. Furthermore, some victims may be more likely to report cases when their awareness of reporting channels is higher following maritime security organisations’ publicity campaigns.
In sum, statistical analysis may not always reflect the actual magnitude of the situation and how it affects different sections of the diverse maritime world – shipping and coastal communities. The situation may be under control for the shipping communities. However, the threat level for coastal communities may continue to be on the high side.
INSIGHTS FROM CASE PATTERNS
Scrutinising patterns in PAR cases instead of statistics only could provide a better situational assessment in terms of economic loss, level of violence used, the profile of pirates, types of ships targeted, who are the owners of the ships, whether the targeted ships were underway or at anchorages, time of the incident, etc. PAR cases should also be analysed alongside other maritime crimes. The overall maritime crime situation may continue to be of concern even if the PAR situation appears to be statistically under control.
Fewer PAR cases may not mean an improvement if perpetrators shift from petty thefts (ReCAAP CAT4 incident) to incidents that involve more violence and economic loss (ReCAAP CAT3 incident). In such a scenario, the pirates are less opportunistic but more organised in target selection, material and other backend support. Instead of the situation under control, the PAR network (e.g. better pirate leaders and recruiters, support from corrupt officials, ready buyers for stolen cargo, etc.) is evolving, therefore, enabling pirates to shift to higher risk but higher reward activities. Counter-piracy measures such as the Malacca Straits Sea Patrol (MSSP) would be insufficient as they could only “control” PAR at sea but not the chain of illicit activities on land that makes the crime possible.[xx] Maritime security agencies should always bear in mind that “all maritime piracy begins and ends on land.”[xxi]
In SOMS, data analytics by ReCAAP suggest that the trend of PAR cases is consistent over the past decade in terms of economic loss and level of violence.[xxii] However, more cases are happening at the Singapore Strait. Several factors may explain this geographic shift. Firstly, the counter-piracy measures along the Malacca Strait may be forcing pirates to “change jobs” to other maritime crimes and shift their operations to the Singapore Strait. Secondly, pirates may be adjusting their strategies to capitalise on better criminal opportunities arising from the growing shipping traffic at the Singapore Strait. Thirdly, it is plausible that more Indonesians in the Riau Islands resort to crime as the province’s economy, particularly Batam, has declined over the past few years and resulted in empty shipyards and rising unemployment.[xxiii]
In this regard, a ReCAAP report stated that the arrests of pirates in 2018 included two masterminds in Batam, a known “pirate haven.”[xxiv] Research unveiled that some Indonesians in the Riau Islands who work as fishermen, boat operators or migrated to Batam from other parts of Indonesia might resort to PAR when in financial desperation.[xxv] Indeed, one measure of whether PAR is under control is to examine if PAR “is still viable for traditional maritime peoples” when “in times of economic hardship.”[xxvi]
Fewer PAR cases may also not mean a real improvement if circumstances make it less risky or more lucrative for pirates and potential pirates to participate in other maritime crimes such as smuggling, IUU fishing and illegal migration. For example, the eight recorded cases in SOMS in 2010 created the perception that PAR there was under control. However, research unveiled that other criminal activities in SOMS “continued unencumbered.”[xxvii]
The number of PAR cases in SOMS for 2016 to 2018 is lower compared to the period of 2011 to 2015. However, the United Nations Office of Drugs and Crime (UNODC) in 2018 reported that the Malacca Strait continues to be a regular human smuggling route for Indonesians travelling illegally to Malaysia.[xxviii] Furthermore, Indonesian and Malaysian authorities reported a shift in the “pattern of drug smuggling” in SEA, given a “high number of drug smuggling attempts” thwarted at the Malaccan Strait.[xxix] Local smugglers are believed to be involved in the short legs of the smuggling operations. As circumstances change, these smugglers may shift or revert to PAR to maintain their earnings with ease as PAR, and other maritime crimes require the same skillsets and tools.
In sum, fewer PAR cases may not be due to the situation being under control but suggests a plausible interaction with other illicit activities at sea.[xxx] PAR statistics are unable to show how pirates are adapting their strategies to “operate within the layers of international policing and surveillance strategies.”[xxxi]
PIRATES’ INFLUENCE OVER PAR SITUATION
The notion that counter-piracy measures could categorically “control” the PAR situation is problematic. It overlooks the fact that the underlying causes of the persistence of PAR have social, economic, environmental and political roots, which such measures have limited control over.[xxxii] The endemic nature of PAR in SOMS suggests that these underlying causes sustain the pirates’ strategies in the maritime world.
The pirates may be “business as usual” despite existing counter-piracy measures as they could adapt their strategies to stay ahead of challenges to their trade. Furthermore, maritime security agencies have to restrict counter-piracy measures due to sovereignty concerns of coastal states. For example, naval patrols remain coordinated instead of joint, leaving gaps at seas, particularly areas where maritime boundaries are unclear, which pirates could exploit to escape hot pursuit. Geopolitical issues create a trust deficit that prevents coastal states from progressing from strategic cooperation (e.g. “talk shops” and capacity building) to substantive operational cooperation among themselves and with other maritime states such as the United States and Japan.[xxxiii] Intelligence sharing may not be optimal as countries such as Indonesia fear that it could reveal “blind spots in intelligence gathering” and that ports in Singapore and Malaysia would benefit disproportionately from Indonesia’s monitoring of shipping lanes.[xxxiv]
Pirates, however, do not frame their activities according to territorial boundaries and the associated restrictions to operations. Instead, they frame their activities according to “targets, objectives and outcomes”, which influence their modus operandi.[xxxv] Research shows that there are three types of PAR from the perspective of pirates who operate in SOMS.
Firstly, “shopping” is a form of simple, opportunistic or hit-and-run case. Pirates would watch the waterways of SOMS from their villages and strike when they feel that the time, target (ship) and environmental conditions are right. Cases of “shopping” may evade detection, and pirate gangs may elude enforcement actions due to several reasons. Pirate gangs could have bribed the local authorities to “look the other way.” The pirates may gain the acquiescence of the coastal communities by portraying themselves as “Robin Hood” and channelling some of the criminal gains to local needs. These local needs include maintaining village mosques, helping locals with medical costs and even donations to political campaigns. Pirates may also dissuade their victims (e.g. ship’s crew) from reporting the cases to the local authorities. They would limit their use of force as long as the victims do not put up a fight. These reasons suggest that pirates do have some control of the PAR situation by sustaining the sentiments among coastal communities that PAR is “culturally thinkable.” Also, the pirates appear to maintain some tacit agreement with victims. The latter would not resist and report cases to the authorities as long as the former limits the use of force and economic loss.[xxxvi]
Secondly, “black business” is a form of professional theft that typically involves the illicit ship-to-ship transfer of fuel or products and the involvement of insiders. This theft is less risky as compared to “shopping” and more likely to evade counter-piracy measures. The lucrative nature of this crime stems from pirates having the resources and connections to bribe local authorities into reducing patrols in the areas that “black business’ activities happen. “Black business” is possible as pirates work with the “networks of corruption on land as well as at sea” and the transnational network of criminal syndicates. These syndicates facilitate the planning and preparation of PAR activities and disposal of stolen fuel and products.[xxxvii]
Pirates could gain the cooperation of insiders – such as crewmembers – in exchange for money because the “Open Register” in the flag state regime is lacking in terms of enforcing “welfare, training and payment of seafarers.”[xxxviii] Furthermore, the lack of training also begs the question of whether the International Ship and Port facility code (ISPS) has “degenerated into a box-ticking exercise” for some ships and particularly on the code’s requirement for “training drills and exercise on ship security.”[xxxix]
“Black business” is a good PAR model. Although the economic loss is higher than “shopping”, violence is unnecessary. The economic loss is within the “margins of error” in product quantities that companies would write off typically as part of the standard accounting process. These reasons mean that “black business” is essentially under-reported and create the impression that local authorities are categorically in control of the situation.[xl] There were arrests of pirates involved in “black business”, but they could also influence the situation by moderating their activities when prices of fuel and commodities are low.[xli]
Thirdly, “perompakan/bajak laut” is a form of PAR that is more violent and resembles the typical imagery of a pirate attack. It involves either the temporary hijacking of a ship to steal its fuel and cargo or the permanent hijacking of a ship to transform it into a phantom ship. The surge in “perompakan/bajak laut” cases in the early 2000s resulted in the implementation of various counter-piracy measures such as Operation MALSINDO.[xlii] Given the risks of interdiction, pirates who wish to continue with their criminal profession, either full time or to supplement their day jobs, have possibly shifted to less risky forms of PAR – “shopping” and “black business.” “Perompakan/bajak laut” could nevertheless increase if there is increasing competition among pirates for targets for “shopping” and “black business.”
However, it is in the interest of the pirate community to keep “perompakan/bajak laut” cases low. This form of PAR is extremely high risk and less sustainable than “shopping” and “black business.” According to some pirates operating in SOMS, PAR activities that are too aggressive and similar to the “Somali business model” are “bad for business.” They attract too much attention from local authorities of coastal states and security forces of maritime states.[xliii] Pirates may also try to evade attention when committing “perompakan/bajak laut” by targeting ships, which are involved in illicit activities and, in particular, “black business.” This scenario is possible if accomplices whom the pirates engage to provide “security overwatch” for “black business” are also involved in providing similar services for “perompakan/bajak laut.”[xliv] Essentially, pirates have their sources of intelligence from within the criminal fraternity.
While maritime security agencies use counter-piracy measures to control the PAR situation, pirates also seek to influence the situation. They would want to ensure that the environment remains favourable for the piracy business in the long run. In terms of strategic thinking, pirates perceive counter-piracy measures as operational obstacles. They seek to overcome the obstacles by adjusting internal factors such as their “targets, objectives and outcomes” and adapting to external, pull and push factors such as economic conditions and commodity prices.
In sum, while statistics may suggest that PAR is under control, it may be “business as usual” for the pirates, as research has suggested. This scenario stems from the possibility that pirates continue to remain active in sea-related illicit activities – which counter-piracy measures may not address – to maintain some influence in the shipping and coastal communities.
CONCLUSION
Media reports often cite counter-piracy measures such as coordinated patrols as the reason for fewer PAR cases in SOMS. Statistics that show fewer PAR cases are usually the primary indicator for the effectiveness of these measures in controlling the situation. However, the reality is that PAR is a persistent problem in SOMS.
The reliance on statistics only can be problematic as it overlooks historical trends and qualitative aspects such as patterns in cases. Furthermore, the “control” of the PAR situation, like a coin, has two sides. On the one side, counter-piracy measures address the symptoms and tactical aspects rather than the underlying causes of PAR. On the other side, these enduring underlying causes sustain the pirates’ strategies in the maritime world. Economic hardships resulting from prolonged COVID-19 pandemic could aggravate these underlying structural causes.[xlv]
To conclude, the PAR situation in SOMS is complex. It entails the interplay between conventional security (symptoms and tactical aspects) and human security (underlying structural causes) factors. The persistence of PAR in SOMS is both a function of counter-piracy measures and the substitution of PAR with viable cultural and economic alternatives for coastal communities in the Riau Islands and along SOMS.
[i] Lim Min Zhang, “Less piracy, armed robbery in Asia waters but vigilance still key.” The Straits Times, January 17, 2019. https://www.straitstimes.com/singapore/less-piracy-armed-robbery-in-asia-waters-but-vigilance-still-key
[ii] ReCAAP, “Monthly Report: Piracy and Armed Robbery against Ships in Asia,” Regional Cooperation Agreement on Combating Piracy and Armed Robbery, January 2020, https://www.recaap.org/resources/ck/files/reports/monthly/2021/ReCAAP%20ISC%20May%202021%20Report.pdf, pp. 8 -11
[iii] ReCAAP, “Monthly Report: Piracy and Armed Robbery against Ships in Asia,” Regional Cooperation Agreement on Combating Piracy and Armed Robbery, May 2021, https://www.recaap.org/resources/ck/files/reports/monthly/2021/ReCAAP%20ISC%20Report%20for%20April%202021.pdf, pp. 9 – 12
[iv] Dale Wainwright, “Piracy at ’27-year low’ but risk remains, warns IMB,” TradeWinds, July 13, 2021, https://www.tradewindsnews.com/casualties/piracy-at-27-year-low-but-risk-remains-warns-imb/2-1-1039215
[v] Ian Storey, “Will Covid-19 Trigger a Tsunami of Maritime Crime in Southeast Asia?” Fulcrum, August 06, 2020, https://www.iseas.edu.sg/media/commentaries/will-covid-19-trigger-a-tsunami-of-maritime-crime-in-southeast-asia/
[vi] Adam McCauley, “The Most Dangerous Waters in the World.” TIME, September 22, 2014. http://time.com/piracy-southeast-asia-malacca-strait/
[vii] Malcolm Davis, “China’s ‘Malacca Dilemma’ and the future of the PLA.” Asia Dialogue, November 21, 2014. http://theasiadialogue.com/2014/11/21/chinas-malacca-dilemma-and-the-future-of-the-pla/
[viii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 123
[ix] Bruce A. Ellermen, Andrew Forbes and David Rosenberg, Piracy and Maritime Crime: Historical and Modern Case Studies. Newport: Naval War College, 2011, p. 81
[x] “Speech by Dr Tony Tan Keng Yam, Deputy Prime Minister and Co-ordinating Minister for Security and Defence at the 2004 IDSS Maritime Security Conference held on Thursday, 20 May 2004 at 9.00 am at Marina Mandarin Hotel,” MCI Singapore, May 20, 2004
[xi] Graham Gerard Ong-Webb, Piracy, Maritime Terrorism, and Securing the Malaccan Straits. Singapore: ISEAS Publishing, 2006, p. 225
[xii] ReCAAP, “ReCAAP ISC Weekly Report: 5-11 Mar 19.” ReCAAP Information Sharing Centre, March 11, 2019. http://www.recaap.org/resources/ck/files/reports/weekly/2019/ReCAAP%20ISC%20Weekly%20Report%20(5-11%20Mar%2019).pdf
[xiii] ReCAAP, “Monthly Report: Piracy and Armed Robbery against Ships in Asia,” Regional Cooperation Agreement on Combating Piracy and Armed Robbery, April 2021, pp. 9 – 12, https://www.recaap.org/resources/ck/files/reports/monthly/2021/ReCAAP%20ISC%20Report%20for%20April%202021.pdf
[xiv] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 12
[xv] Stefan Eklof, Pirates in Paradise: A Modern History of Southeast Asia’s Maritime Marauders. Copenhagen: NIAS Press, 2006, p. 51
[xvi] Derek Johnson and Mark Valencia (Eds.), Piracy in Southeast Asia: Status, Issues and Responses. Singapore: ISEAS Publications, 2005, p. 24
[xvii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, pp. 16 – 18
[xviii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 2
[xix] Euan Graham, “Syphoning Confidence: Piracy and Fuel Theft in Southeast Asia.” RSIS Commentary, November 18, 2014. https://www.rsis.edu.sg/wp-content/uploads/2014/11/CO14227.pdf
[xx] Karsten Von Hoesslin, “The Economics of Piracy in Southeast Asia.” Global Initiative against Transnational Organized Crime, May 2016, p. 21
[xxi] Bruce A Ellermen, Andrew Forbes and David Rosenberg, Piracy and Maritime Crime: Historical and Modern Case Studies. Newport: Naval War College, 2011, p. 81
[xxii] ReCAAP. (2018). “Annual Report 2018: Piracy and Armed Robbery Against Ships in Asia.” ReCAAP Information Sharing Centre, December 31, 2018. http://www.recaap.org/resources/ck/files/reports/annual/ReCAAP%20ISC%20Annual%20Report%202018.pdf, pp. 50 -55
[xxiii] Francis E. Hutchison and Siwage D. Negara, “Batam’s Emerging Digital Economy: Prospects and Challenges.” ISEAS Yusof Ishak, April 10, 2019. https://www.iseas.edu.sg/images/pdf/ISEAS_Perspective_2019_25.pdf, p. 3
[xxiv] Eric Frecon, “Beyond the Sea: Fighting Piracy in Southeast Asia.” RSIS Commentary, December 21, 2009. https://www.rsis.edu.sg/rsis-publication/rsis/co09128-beyond-the-sea-fighting-piracy-in-southeast-asia/#.YMgYDvLivIU
[xxv] Eric Frecon, “Pirates with black magic attack shipping in Indonesian waters.” The Conversation, April 27, 2018. http://theconversation.com/pirates-with-black-magic-attack-shipping-in-indonesian-waters-94106
[xxvi] Bruce A Ellermen, Andrew Forbes and David Rosenberg, Piracy and Maritime Crime: Historical and Modern Case Studies. Newport: Naval War College, 2011, p. 82
[xxvii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p.122
[xxviii] UNODC, “Global Study on Smuggling of Migrants 2018.” United Nations Office on Drugs and Crime, June 2018. https://www.unodc.org/documents/data-and-analysis/glosom/GLOSOM_2018_web_small.pdf, p.127
[xxix] Apriadi Gunawan, “Malacca Strait remains prone to transnational crimes.” The Jakarta Post, December 05, 2018. https://www.thejakartapost.com/seasia/2018/12/05/malacca-strait-remains-prone-to-transnational-crimes.html
[xxx] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p.169
[xxxi] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p.122
[xxxii] Derek Johnson and Mark Valencia (Eds.), Piracy in Southeast Asia: Status, Issues and Responses. Singapore: ISEAS Publications, 2005, pp. 25 and 126
[xxxiii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, pp. 170 – 171
[xxxiv] Karsten Von Hoesslin, “The Economics of Piracy in Southeast Asia.” Global Initiative against Transnational Organized Crime, May 2016, p. 20
[xxxv] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 124
[xxxvi] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, pp. 124 – 126
[xxxvii] Karsten Von Hoesslin, “The Economics of Piracy in Southeast Asia.” Global Initiative against Transnational Organized Crime, May 2016, pp. 11, 15 and 21
[xxxviii] Carolin Liss, “The Roots of Piracy in Southeast Asia”, Nautilus Institute, October 22, 2007. https://nautilus.org/apsnet/the-roots-of-piracy-in-southeast-asia/, p. 5
[xxxix] Derek Johnson and Mark Valencia (Eds.), Piracy in Southeast Asia: Status, Issues and Responses. Singapore: ISEAS Publications, 2005, p. 37
[xl] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, pp. 126, 127 and 169
[xli] Karsten Von Hoesslin, “The Economics of Piracy in Southeast Asia.” Global Initiative against Transnational Organized Crime, May 2016, pp. 20 – 21
[xlii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 128
[xliii] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 124
[xliv] Liss and Biggs (Eds.), Piracy in Southeast Asia: Trends, Hot Spots and Responses. New York, NY: Routledge, 2017, p. 129
[xlv] CNA, “Sea robbery incidents in Singapore Strait rise again in 2020,” Channel News Asia, January 15, 2021, https://www.channelnewsasia.com/news/singapore/singapore-strait-sea-robbery-piracy-13966858


