Since the time of Empress Wu Chao, who created the first Chinese intelligence service in 625 A.D., much has changed, but we could also say that some traits have not completely changed, as we might believe at first sight.
Later there was China’s extraordinary adventure in the modern world, which began with the fall of the last Emperor Pu Yi, who was also guilty of collaborationism with the Japanese in Manchukuo and ended his days artistically drawing the phrase “today the people are sovereign” at the court of Mao Zedong.However, as early as 1934, the British intelligence Services deciphered MASK, the code used by the Komintern to encode information from Moscow to Shanghai which, at that time, was the CPC’s pole.
However, it was in 1957 that the United States began to fly its U-2s over China, starting from Peshawar.
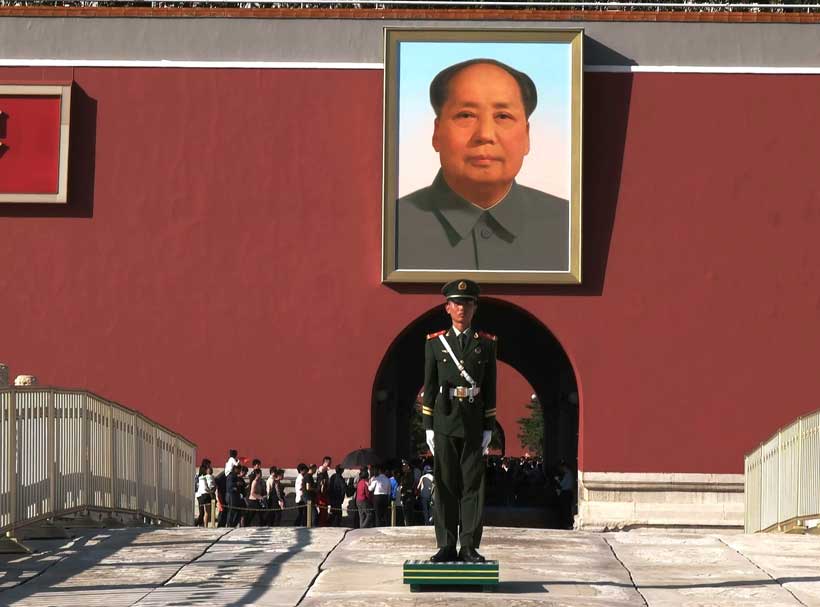
In 1966, two years after the beginning of the Great Cultural and Proletarian Revolution, there was the great purge of the intelligence services in China carried out by the very powerful Kang Sheng. He was the mover of the fall of Liu Shaoqi, Deng Xiaoping and Lin Biao, but then he was associated with the “Gang of Four” and hence suffered the usual damnation memoriae. A man of Mao Zedong who knew too much, but died in his bed.
Then, as is well-known, in 1971 Li Biao was killed while fleeing to the USSR with his plane.
Not surprisingly, again in 1971, Kissinger began to deal secretly with China. Lin Biao’s death was the seal on the definitive strategic separation between China and the Soviet Union – which was what the United States was interested in.
In 1973 the first CIA “station” was created at the U.S. liaison office in Beijing, while China took the Paracel Islands and CIA left its main station in Taiwan.
In 1975 the first Chinese Electronic Intelligence satellite (ELINT) was launched, but the following year saw the death of Zhou Enlai, the true master of Chinese foreign policy and Kissinger’s friend who protected Mao from his mistakes.
The Armed Forces returned to power: with the support of all the military, Deng Xiaoping quickly put Hua Guofeng aside and became the CPC Secretary, but reforms were still being studied. Initially Deng was not as reformist as currently believed in the West.
Hence in Deng’s reformist phase, the U.S. diplomatic recognition was shifted from Taiwan to the People’s Republic of China – and that was China’s real goal at the time.
Shortly afterwards, China also opened diplomatic offices in the United States.
In 1981, however, the Americans developed programmes for controlling the Chinese agents operating in the USA, while Deng Xiaoping himself started China’s nuclear rearmament.
The China National Nuclear Corporation was established in 1988.
Ten years later, in 1999, the Chinese Armed Forces built a base for intercepting military signals in Cuba but, in 2002, the Chinese cyber attacks on some U.S. networks – known as TITAN RAIN – began, while the FBI even opened a liaison office in Beijing, with assignments also extended to Mongolia.
In 2004, China put the Nanosatellite I into orbit, but there was also a further cyber attack – probably of Chinese origin – on the U.S. Army Information Systems Engineering Command, as well as on the Naval Ocean Systems Center, and finally on the space and strategic installation in Huntsville, Alabama.
In 2010, Google suffered an AURORA cyber attack. A long, powerful and initially uncontrollable attack.
Probably also Symantec, Northrop Grumman, Morgan Stanley and Dow Chemical were hit by AURORA cyber attacks – albeit this fact is not confirmed.
Hence data collection, mainly economic and technological intelligence for China, but also a complex relationship with the United States to be penetrated informally, but not to be damaged too much.
In any case, the reins of the Chinese Service (or rather, the intelligence services) were held by the State Security Ministry.
A legal difference should be underlined: while, legally speaking, the KGB was a Central Committee’s Department, the Communist China’s intelligence Service was a real Ministry.
The Interior Ministry was represented by the Public Security Ministry but, in general terms,it should be said that – unlike the old Soviet ones – the Chinese intelligence Services are less obsessive in their relationship with possible “sources”, anyway preferring ethnically Chinese people.
Furthermore, the Chinese Foreign Service seems to prefer sources that – unlike what happened with the Soviet KGB – have no money or personal crisis problems, which become dangerous or ambiguous.
Again unlike the old Soviet ones, the Chinese intelligence Services do not willingly pay for news and information. They do not blackmail and they do not extort. Quite the reverse. They do not pay at all. If anything, they help Chinese abroad for relatives or other matters.
Hence rarely do the Chinese intelligence Services pay for the data they receive.
The Chinese intelligence Agencies are therefore interested in people who,only rarely, come within the range of attention of the enemy intelligence Services. Operationally speaking, this is an excellent choice.
Again unlike the old Soviet ones, China’s intelligence Services do not organize rezidenture abroad. They also rarely hold clandestine meetings and almost never use covert communications.
“The floating bird is existence, if it dives it is non-existence”. The mind is like the moon: it is reflected in the water at a speed that man does not perceive. The mind should not be stopped, but left free to grasp the void, the invisible, the Nothing.
The Chinese intelligence Services, however, organize closed areas where a “source” finds itself – with its pace and needs – providing the materials needed by the Chinese government.
The width of the network, however, is such that the slow and non-invasive pace of Chinese operatives is capable of reaching the same – or even larger – quantity of sensitive material collected by a Service that does not follow the Tao, i.e. the natural flow of events and people.
Moreover, the Chinese intelligence Service often operates with real academics, real students, real journalists and very real businessmen.
The cover is often irrelevant, but also very true. Indeed, it is considered a cover attracting excessive interest – like jealousy which, as Karl Kraus used to say, “is a dog’s bark which attracts thieves”.
Obviously, in this respect, the Chinese intelligence Services have a significant advantage, since they can legally use real journalists and real academics, while in the West – including in Italy – it is forbidden to use “journalists, clergymen, parliamentarians and town councillors” as agents. Stupidity has been tormenting the intelligence Services with a ferocity worthy of a better cause.
Hence no one who can really be useful. This leads the Western intelligence services to fabricate useless complicated “stories” that are often easily discovered by the adversaries.
Not to mention the forty-year defamation of the intelligence Service – as is the case in Italy – which causes other damage.
For the intelligence Services, the Chinese technological companies operating in the West must be economically self-sufficient and, indeed, make profit, without weighing on the Service’s or State’s coffers.
An often predatory “Western-style” profit is also allowed, at least as long as this does not negatively affect intelligence operations.
Therefore, the Chinese companies using up technology and data – which are the primary material of current Chinese intelligence – must be the most obvious and natural enterprises, without hidden compartments or ambiguous operatives that the host country’s intelligence Services can discover – albeit possibly not so easily.
Another problem in the control of Chinese operations in the West is the difficulty – and, indeed, we could say the reluctance- with which our companies, including SMEs, report the often harshly blackmailing cyber attacks, or even the crises resulting from fraud and scams often carried out by managers and employees.
The obsession of being always listed on the Stock Exchange makes companies, including the small and medium-sized ones, excessively afraid of disclosing such adverse operations.
According to Leonardo-Finmeccanica, during the Covid-19 phase, there have been 230,000 malspam operations worldwide, 6% of which in Italy.
This year 51% of all Italian companies have suffered one or more significant cyber attacks, with a 125% average expansion for the domains called “Covid”.
In China, however, there has recently been a change of the State system.
While in the past, before globalization, also thanks to an “imperial” psychology, the Service had above all to defend borders and, to some respects, also the “purity” of the Chinese ethnic balance, today – considering the global economic role played by China – the Service has to deal with 1) the security of raw materials supplies from abroad and 2) the stability of the productive system in a phase of great social transformations.
Hence the necessary current complexity of the Chinese Party’s and State’s decision-making system: the top level is the National Security Leading Small Group (NSLSG), which also has many informal strategic decision-making mechanisms within the Chinese ruling class. An elite that has always been more informal than we might think.
Certainly, at institutional level, there is also the Politburo Standing Committee, but there is still Hu Jintao, a man still essential to the power architecture of Xi Jinping, who listens to him carefully.
There is also the Foreign Affairs Leading Small Group, which is less involved in relations with the United States – of which the aforementioned National Security Leading Small Group is in charge – but mainly controls the work of the Agencies and connects them.
In addition to the intelligence Services’ role, a fundamental role is also played by the various and often excellent academic and non-academic think tanks.
Also the results of these structures are assessed by the Small Groups.
But how is foreign policy decided in China?
First of all, there is the CPC but, more precisely, the “Politburo Central Committee”, in addition to the aforementioned Politburo Standing Committee (PBSC).
With its 204 members and 167 “alternate” members, the Central Committee meets once a year.
The “Politburo Central Committee” is composed of 25 members, elected by the Central Committee. It meets once a month and five of its members do not usually live in Beijing.
The PBSC, the Central Committee Standing Group for Foreign Affairs, meets once a week and has nine members.
The Meeting is often coordinated by the Central Committee’s Foreign Affairs Office.
Within the Standing Committee, the Foreign Affairs Office has a specific area responsibility, but we should not think that Chinese Communism is authoritarian, at least in the childish sense of the term.
The bigger the issue, the wider and freer the discussion. The leader’s policy line is always to buildthe broadest consensus among his advisers.
With specific reference to the thorniest issues, the leader often appoints a “first collaborator” but usually the “central” meetings are routine for minor issues, even geopolitically, while the leader speaks and decides on the essential issues: the relations with the United States – still a constant obsession of the Chinese intelligence Service – with Japan, Taiwan or, most likely, the Russian Federation.
The policy line at the top of the decision-making system – and this also pleases Xi Jinping – is still the old and stable policy line developed by Jang Zemin, which was defined in 1999: “collective leadership, democratic centralism, individual preparation and decisions that always result from meetings”.
In this way, the Standing Committee and the Central Committee’s Foreign Affairs Office prepare briefings and distribute them among the Central Committee’s offices.
Often there is no voting, but discussions are held until consensus is reached.
For example,a rare case of voting was when North Korea conducted a nuclear test in 2009 and China had to decide whether to withdraw its support for the country. Seven negative votes were cast against support for North Korea.
The establishment of the aforementioned National Security Leading Small Group (NSLSG)mainly followed the U.S. bombing of the Chinese Embassy in Belgrade.
A fact that has marked China’s recent political history.
Hu Jintao, whom the PSBC defined as a “main personality”, leads a complex office: eight Ministers from the State Council; two from the Foreign Ministry; the National Security Minister; the Minister of Commerce; the Taiwan Affairs Office, the Office dealing with Hong Kong and Macao; the Overseas Chinese Affairs Office and finally the Information Office.
There are also two Party’s bodies: the Propaganda Department and the International Department.
The Armed Forces are represented by the Defence Minister and the Chief of Staff.
Therefore, the Chinese intelligence Services have a completely different style and modus operandi compared to the Westerners’ intelligence practices. They also have a complex and technically refined organization of political control over the Services’ operations, and finally a different finalization of the Chinese Agencies’ operations in the West, at least for the time being.