The threat of cyberwarfare is a growing fear among all intelligence communities. “In June 2009 the U.S. Cyber Command was created and in July of 2011 Deputy Secretary of Defense William J. Lynn III announced that as a matter of doctrine, cyberspace will be treated as an operational domain similar to land, air, sea, and space” (Colarik & Janczewski, 2012, 35). Cyber warfare is conducted by infiltrating the country’s computer networks to cause damage and/or disruption to various infrastructures. This could be as minimal as spying on another nation or as in-depth as implementing acts of sabotage directed towards specific targets such as military operations or the power grid. The threat of cyber warfare is not specific to one country. This is a potential threat that effects each country across the globe.
China is a dominant power within the global arena and is consistently evolving with potential threats especially cyber technology. Chinese colonels Liang and Xiangsui claimed advanced technology gave the country’s adversaries a significant advantage, and proposed that China ‘build the weapons to fit the fight. Recently, the Chinese People’s Liberation Army (PLA) confirmed the existence of its Online Blue Army (Colarik, &Janczewski, 2012, 35). China’s fear of the impact and devastation that can be caused by the internet has forced them to implement strict policies governing the freedom and use of the internet within the country and creating strong security measures against infiltration by outside sources.
In 2014, China implemented the Central Internet Security and Informatization Leading Group to oversee all internet security. “This leading group is to deepen reform, protect national security, safeguard national interests, and promote the development of information technology. The group will have complete authority over online activities, including economic, political, cultural, social, and military” (Iasiello, 2017, 5). This group disseminates and monitors all information found on the web to ensure that there are no security breaches and the people are not in violation of the law.
In 2015, China drafted a national cybersecurity law.“The chief goals of its 2015 draft national cybersecurity law are (1) ensure cybersecurity, (2) safeguard cyberspace sovereignty, national security, and the public interest, (3) protect the legitimate rights and interests of citizens, legal persons and other organizations, and (4) promote the healthy development of economic and social information” (Kolton, 2017, 126). Whereas the United States promotes a free internet, China’s main focus is on establishing an internet that is secure from all potential threats both external and internal.
In 2016, China passed the “Cyber Security Law” that focused on the security of the internet and information systems and extended the ability of the government to oversee the information that was being shared to determine if it was done within accordance of their strict cyber security laws. This law helps the government to monitor any potential breaches of security by outside or internal sources. By implementing a stronger grasp of control over the internet, the government is able to reduce the potential of an attack or intrusion. Within this law, government agencies would be able to implement more guidelines for network security within industries to include energy, transport, military, defense, and many more (Iasiello, 2017, 6).These restrictions increase the control of the government over cybersecurity but also limits the freedoms of its citizens to explore the internet.
China has created new training for its military to be prepared against potential cyber warfare attacks. It has “developed detailed procedures for internet warfare, including software for network scanning, obtaining passwords and breaking codes, and stealing data; information-paralyzing software, information-blocking software, information-deception software, and other malware; and software for effecting counter-measures” (Ball, 2011, 84). It has also increased its number of training facilities to focus only on network attacks on cyber infrastructure and defense operations. The amount of money China is investing in facilities and training of military personal increases its ability to remain secure within this global threat of cyber warfare. One fear for China is its dependence on Western technology. “China’s capabilities in cyber operations and emerging technologies such as artificial intelligence are becoming more sophisticated, the country still depends largely on Western technology. Beijing is hoping to break that dependency through the Made in China 2025 plan” (Bey, 2018, 33). This is a mutual fear for both the US and China as they both rely on each other’s manufacturers with the fear that they will implement a trojan horse to intervene.
Like China, Russia has increased its abilities in combating the potential threat of cyber warfare. However, Russia has taken a different approach to this threat by going on the offensive. Russia has focused on non-linear warfare within the cyber world, which is defined as “the collection of plans and policies that comprise the state’s deliberate effort to harness political, military, diplomatic, and economic tools together to advance that state’s national interest. Grand strategy is the art of reconciling ends and means” (Schnauffer, 2017, 22). To assert its dominance in the global arena, Russia has been utilizing its own forms of cyber attacks to collect information and become a dominant cyber power.
Russia began its experiments with cyber warfare in 2007 in the clash with Estonia. This was done to determine its cyber capabilities as well as create a stronger resilience against future attacks. “Russia’s cyber experiment effectively shut down day-to-day online operations in Estonia’s cyber infrastructure for weeks, from news outlets to government institutions” (Shuya, 2018, 4). After this successful movement, Russia began to expand its focus to Georgia and Ukraine in 2008 and then in 2015, to offset local initiatives there which it considered to be against Russian national security interests. Russia has “developed multiple capabilities for information warfare, such as computer network operations, electronic warfare, psychological operations, deception activities, and the weaponization of social media, to enhance its influence campaigns” (Ajir& Valliant, 2018, 75). Russia has had a strong focus on using the tool of propaganda to disseminate key information to its citizens with the hope that they will abide by it as the real truth.
Russia’s investment into technology and the freedom of speech allotted by the West has made the West not only extremely vulnerable to Russia, but also has expanded the reach of the Russia globally. Ajir and Valliant (2018) highlight several key points of the Russian strategy:
Direct lies for the purpose of disinformation both of the domestic population and foreign societies; Concealing critically important information; Burying valuable information in a mass of information dross; Simplification, confirmation, and repetition (inculcation); Terminological substitution: use of concepts and terms whose meaning is unclear or has undergone qualitative change, which makes it harder to form a true picture of events, Introducing taboos on specific forms of information or categories of news; Image recognition: known politicians or celebrities can take part in political actions to order, thus exerting influence on the worldview of their followers; Providing negative information, which is more readily accepted by the audience than positive.
This approach allows the Russian government to remain in control of information that is filtered to its citizens. The restriction of freedom reduces the capability of deciphering fact from fiction.
Russia has also taken a defensive approach to cyber warfare by implementing strict laws that govern the use of the internet. The agency Roskomnadzor scans the internet for activity that is deemed illegal and detrimental to the Russian government. It has also implemented new laws to regulate internet activity. “The laws which came into force in November 2012 provided provisions for criminalizing slander, requiring nonprofits receiving funding from abroad to declare themselves “foreign agents,” and provide additional financial information and a final law sanctioning the blocking of websites featuring content that “could threaten children’s lives, health, and development” (Cross, 2013, 14). Many have deemed these laws as means to censor the internet, but the Russian government argues it is for the protection of its citizens.
An opposite example of failing to employ measures to protect the country from a potential cyber warfare attack is Mexico. The main focus for Mexico has been on drug cartels and eliminating internal threats within their own government. Mexico has begun to implement its own version of cybersecurity due to its substantial growth in cyber-attacks over the years. However, its overall success has been limited due to a lack of understanding and outdated systems. “Incidents in cyberspace pose a challenge to Mexico due to a lack of institutional structures and there is a need to strengthen capabilities since it does not have any specialized government or public sector agencies certified under internationally recognized standard” (Kobek, 2017, 8). Without the establishment of a specific agency dedicated to cybersecurity, Mexico will continue to struggle against cyber warfare threats. Mexico must implement new security measures that are applicable to all main threats beyond the drug cartels.
Currently, the government presence in Mexico is focused solely on actionable and tangible threats. There must be a reform to its current laws for “the armed forces require a law that reframes and modernizes the concepts of public safety, internal security, and national defense; clarifies the role, conditions, terms, and limits of the armed forces’ engagement; and establishes mechanisms to hold them accountable” (Payan& Correa-Cabrera, 2016, 3). The lack of accountability and oversight by the government to control key aspects, such as the military, and impose a stronger presence in the more demanding field of cybersecurity opens up the potential for a catastrophic event to occur within Mexico.
China and Russia are prime examples of how strict policy governance of the internet will help to reduce the potential threat of an attack. They are micromanaging every aspect of the internet from restricting specific websites (social media) or establishing specific agencies to monitor and analyze all information that is being viewed from all sources. “With the United States and European democracies at one end and China and Russia at another, states disagree sharply over such issues as whether international laws of war and self-defense should apply to cyber-attacks, the right to block information from citizens, and the roles that private or quasi-private actors should play in Internet governance” (Forsyth, 2013, 94). The failure of this policy is the restriction of freedoms to citizens. As stated above, one of Russia’s main focuses is promoting propaganda that is anti-west and pro-Russia. The control over the internet does not allow their citizens to research the truth or have global interaction. This increases the risk of upheavals among the people, especially as technology continues to improve and loopholes are found to circumvent existing policies and hidden content is exposed.
Another approach to cybersecurity is seen with the actions of NATO. It is focusing on improving its relationships with private security companies and “developing a Cyber Rapid Reaction Team (RRT)19 to protect its critical infrastructure, much like U.S. Cyber Command’s Cyber Protection Teams (CPTs)” (Ilves et al, 2016, 130). One downside to this approach is NATO is only able to apply defensive measures. It does not have the ability to implement an offensive attack. Creating a partnership with private companies provides it greater access and resources to potential cyber threats. Private companies have more funds available to pursue a stronger cyber security defense. A recommendation would be to create a joint European Union, United States, and NATO partnership against cyber warfare. Each has its own strengths that can be applied to a joint force against one common threat. A stronger partnership among key global powers will help to create a multifaceted approach to the threat of cyber warfare. The end goal of cyber warfare is the same for each country targeted. There is no specific adversary, but rather the substantial disruption or sabotage of key infrastructure.
Although facing intense criticism and skepticism, it would be beneficial for the US, China, and Russia to form a partnership against cyber warfare. As each country is already connected via their technology companies, they are each a global power that encompasses a vast majority of the world. A collaboration of information and resources would provide a stronger protection amongst common non-state threats. However, the chief obstacle is the ability to trust each country to act within the realm of security, instead of using it as an opportunity to gain substantial access to an inside look of the country. Since the US often accuses China and Russia of being the biggest state perpetrators of cyber actions, this criticism may be near impossible to overcome, despite the possible advantages. According to the World Economic Forum, the table below lists the top countries best prepared against cyber-attacks.
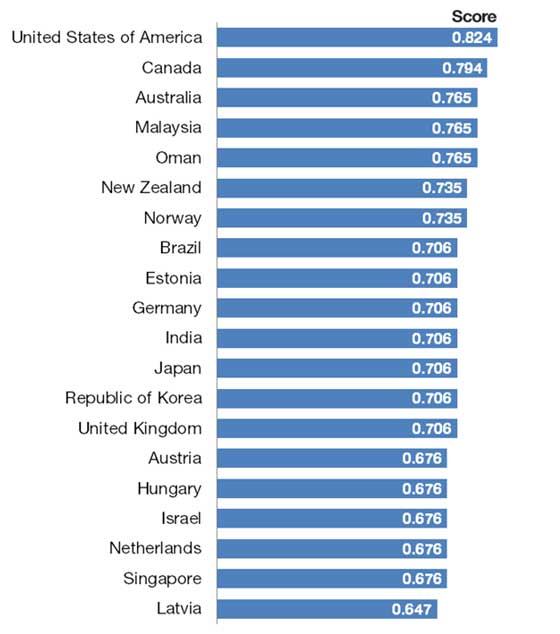
The United States is ranked number one with a significant margin above Canada. China and Russia who have implemented a very strict cyber security policy are not listed within the top 20. This is determined by the Global Cybersecurity Index, a partnership between private industries and international organizations that analyze all aspects of cybersecurity. This argues that the approach by countries such as China and Russia is geared more to the control over its citizens rather than executing a strong cybersecurity policy focused on legitimate external threats. Although, the table above does show that the United States is ranked number one in being able to protect the nation from potential cyber threats, it is only ranked at 82.4% effective. Russia and China have employed a different approach to cyber security that could be utilized to increase the overall effectiveness globally if each side was able to work together towards common threats. Ideally, such partnership would not only create new channels of connection and collaboration between adversaries, but would also set the stage for the more heavy-handed and restrictive policies of China and Russia to be loosened to the benefit of its citizens’ virtual freedom.


