Authors: Lorand Bodo, M.A. & Anne Speckhard, Ph.D.
[yt_dropcap type=”square” font=”” size=”14″ color=”#000″ background=”#fff” ] A [/yt_dropcap]s ISIS is rapidly losing its territory in Syria and Iraq they continue to win on the digital battlefield, maintaining a strong recruiting presence in the digital space[1]. As ISIS cadres inspire and even direct terrorist attacks on different continents, the West must realize that it is long past due to mount a strong and resolute digital battle against ISIS—to stop them radicalizing and guiding the world’s terror plots from afar[2].
To fight terrorist propaganda on the Internet, social media companies, such as Twitter, Facebook and YouTube have all instituted take down policies[3] and teamed up with Microsoft to create a database of unique ‘fingerprints’ to automatically detect terrorist propaganda in the form of images and videos[4]. Additionally, Facebook has recently announced that it would develop Artificial Intelligence (AI) software to review content on their social network[5]. Likewise, Jigsaw—Google’s technology incubator and think tank—came up with a clever approach by utilizing the so-called ‘Redirect Method’[6]. That is, once certain keywords and phrases are typed into Google’s search box, links appear that redirect the user to content that is deemed as effectively countering ISIS’ propaganda[7]. Despite these efforts, however, ISIS still continues to successfully disseminate its propaganda on the internet.
A recent study did find a productivity drop of approximately 36 percent as in contrast to ISIS’ productivity height in the summer of 2015,[8] yet intelligence professionals credit ISIS with five new recruiting videos a week and there was a bump in ISIS propaganda following the London attacks[9]. Likewise, in two recent studies ICSVE research fellows located over the space of only a few hours over 50 English and 70 Albanian speaking ISIS endorsing, spreading and following Facebook accounts.[10] YouTube also continues to host for months at a time numerous ISIS promoting testimonies and videos as documented by a researcher following ISIS propaganda on YouTube.[11] Likewise, as ISIS has found it more difficult to operate in the non-encrypted space they have learned to coax their followers into the encrypted spaces of Telegram, WhatsApp etc. where they are further lead down the terrorist trajectory—encouraged to travel or stay at home to mount terror attacks.
It’s imperative to understand ISIS’s current social media and Internet-based dissemination process before we can judge the effectiveness of existing counter measures. To do so, we conducted a small study on the dissemination of ISIS propaganda on the Surface Web – that is the proportion of the World Wide Web, which is indexed and thus searchable with standard search engines such as Google, Bing, or Yahoo etc.[12]
Based on our previous Facebook research, we used hashtags, keywords and phrases in English and Arabic known to identify ISIS followers, endorsers and distributers on social media. Once again we quickly identified several social media accounts, websites and forums hosting ISIS propaganda. Most interestingly, however, we found that all these sources link back to a single source—what we call the ’Daily Harvester’.
The ‘Daily Harvester’ is a person or group of people that collects official ISIS propaganda, creates and shares a 40 to 80 page ‘daily briefing’ containing everything from pictures to videos to news bulletins. These summaries intend to ‘inform’ ISIS supporters on a daily basis by providing a summary of yesterday’s events, news and media releases. However, these daily briefings have also the potential to radicalize others as well as foster the existing belief system of already radicalized individuals.
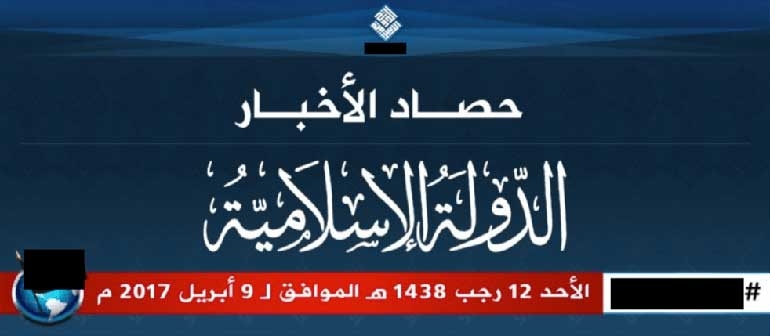
In this case, the Daily Harvester is called Abu Abdellah Al-Ifriqi [أبو عبد الله الإفريقي][13] and even has created his own logo (see Figure 1). We assume that Abu Abddellah is an official ISIS representative.
Figure 1
We monitored Abu Abdellah for approximately one month (March 16 to April 16, 2017) to identify the key phases and tools he uses in the dissemination process (Fig.2).
Figure 2 (Created in Lucidchart)
Four distinct and consecutive phases emerged in observing his activities. First, the Daily Harvester monitors official ISIS media outlets, such as Amaq News Agency or Al-Hayat Media, for example. Second, he then collects published audios, documents, news, photos and videos and puts everything together into a single document. Third, he uploads the briefing onto only two websites – justpaste.it and addpost.it. These ‘paste-websites’ allow anyone to simply paste and publish content on the Surface Web by providing a unique link that can be shared. Finally, the harvester uses the generated link and shares it via social media platforms, forums and other websites to reach out to as many people as possible with a vast compendium of current ISIS propaganda.
Abu Abdellah is not the only Daily Harvester. Daily Harvesters are incredibly dangerous because they spread a huge quantity of ISIS propaganda at the click of a link, making it accessible to anyone. Put differently, anyone who knows how to use Google will be able to find these briefings and it’s a simple matter using Google Translator to read and view them in ones own language. For this reason, we need to take action against these simultaneous compilers and distributors of ISIS materials. If we don’t do that we will see repeats of what happened in London, Stockholm, Nice and Toronto, to name but just a few—as these attacks occurred as a result of Internet enticement into ISIS ranks and thinking.
There is no doubt that this will be an incredibly difficult task, however, based on our analysis, we recommend two strategies for the digital battlefield: First, we need to disrupt the dissemination process and second we need to counter their propaganda by pushing counter-narrative materials that will appeal to ISIS followers and endorsers into the digital spaces where they lurk and currently imbibe of ISIS poison.
Counter-narratives: Using emotionally evocative and strong counter-narrative materials, preferably that rely on ISIS insiders denouncing the group as ICSVE is producing in multiple languages—because we know that ISIS followers narrow their attention to listening only to ISIS insiders[14], we recommend using the same hashtags as used by the ‘Harvester’ to reach out to those who are looking for the daily briefings. Likewise, we recommend using justpaste.it and addpost.it to upload and publish counter-narratives as this would be appealing to those who regularly visit these websites to access the Harvester’s briefings.
Disruptive measures: We recommend the development and use of an automated and artificial intelligence based detection software for social media platforms, in particular Twitter and Facebook. This searches, amongst others, for three things: First, hashtags used by the Daily Harvester and secondly, links provided, such as justpaste.it and addpost.it. Abu Abdullah, the Daily Harvester we studied for example, uses only these two websites. Lastly, we discovered social media that accounts on Twitter and Facebook that disseminated the link, were not permanent and in fact, changed on a daily basis. Therefore, as a final point, we recommend integrating the age of an account as an important indicator for potentially being a disseminator.
Disrupting the link between the website that hosts the content and potential ‘customers’ is more effective than trying to directly take down the Harvesters themselves or the hosting websites. That is due to several reasons: first, Daily Harvesters can be easily replaced. Second, daily briefings can be published on millions of other websites; hence, tackling websites would result in a cat and mouse game. Third, Facebook, Twitter, YouTube, etc. are popular social media platforms and there are little to no alternatives in terms of reaching out to millions of people, which also implies that ISIS will continue to covertly and cleverly attempt to exploit these platforms.
Additionally, fake ‘daily briefings’ could also be uploaded to these sites following the Daily Harvester’s protocols with malware to enable law and intelligence forces to gather sensitive information on those who download the briefings.
ISIS is losing on the battlefield in Syria and Iraq, but is winning in the digital space – we need to adapt and fight back.
Reference for this Article: Lorand Bodo, M.A. & Anne Speckhard, Ph.D. (April 22, 2017) The Daily Harvester: How ISIS Disseminates Propaganda over the Internet Despite Counter-Measures and How to Fight Back. ICSVE Brief Reports. http://www.icsve.org/brief-reports/the-daily-harvester-how-isis-disseminates-propaganda-over-the-internet-despite-counter-measures-and-how-to-fight-back/
[1] McDowell-Smith, A., Speckhard, A., Yayla, A. S. (2017). Beating ISIS in the Digital Space. Focus Testing ISIS Defector Counter-Narratives with American College Students. Journal for Deradicalization, Spring 2017, No. 10, pp.50-76.
[2] Callimachi, R. (2017, Feb 4). Not ‘Lone Wolves’ After All: How ISIS Guides World’s Terror Plots From Afar. Retrieved from https://www.nytimes.com/2017/02/04/world/asia/isis-messaging-app-terror-plot.html
[3] Twitter (2016, Aug 18). An update on our efforts to combat violent extremism. Retrieved from https://blog.twitter.com/2016/an-update-on-our-efforts-to-combat-violent-extremism
[4] Associated Press (2016, Dec 5). Facebook, Microsoft, Twitter and YouTube team up to fight terrorist propaganda. Retrieved from http://www.latimes.com/business/technology/la-fi-tn-internet-terrorism-20161205-story.html
[5] BBC (2017, Feb 16). Facebook algorithms ‘will identify terrorists’. Retrieved from http://www.bbc.co.uk/news/technology-38992657
[6] Unknown Author (2017, Apr 17). The Redirect Method. Retrieved from https://redirectmethod.org/
[7] Greenberg, A. (2016, Jul 6). Google’s Clever Plan to Stop Aspiring ISIS Recruits. Retrieved from https://www.wired.com/2016/09/googles-clever-plan-stop-aspiring-isis-recruits/
[8] Winter, C. (2017, Mar 23). ICSR Insight: The ISIS Propaganda Decline. Retrieved from http://icsr.info/2017/03/icsr-insight-isis-propaganda-decline/
[9] Speckhard personal communication from Belgian Intelligence/OCAM, March 17, 2017
[10] Speckhard, A., Bodo, L., and Shajkovci, A. (under review). Fighting ISIS on Facebook-Breaking the ISIS Brand Counter-Narratives Project; Speckhard, A., Fazliu, H., Bodo, L., and Shajkovci, A. (under review). Bringing Down the Digital Caliphate-Breaking the ISIS Brand Counter-Narratives Intervention with Albanian Speaking Facebook Accounts.
[11] Mehdi Zograib personal communication to Anne Speckhard, March 11, 2017.
[12] Weimann, G. (2016). Going Dark: Terrorism on the Dark Web, in: Studies in Conflict and Terrorism, Vol.39(3), pp.195-206.
[13] Thereafter referred to as ‘he’