Ever since Donald Trump won the elections, the Democrats who have been (or ‘were’) very magnanimous about the fact they would accept the election results whatever be the outcome, have been vigorously demanding an enquiry into the hacking by Russia into their Democratic National Committee (DNC) meetings which resulted in a variety of colorful information about the activities done by the Democrats behind closed doors. Videos released by Project Veritas also showed how the Democratic strategists planted agitators in Donald Trump rallies to incite violence. But that is a different story altogether. Let’s get back to the curious case…..
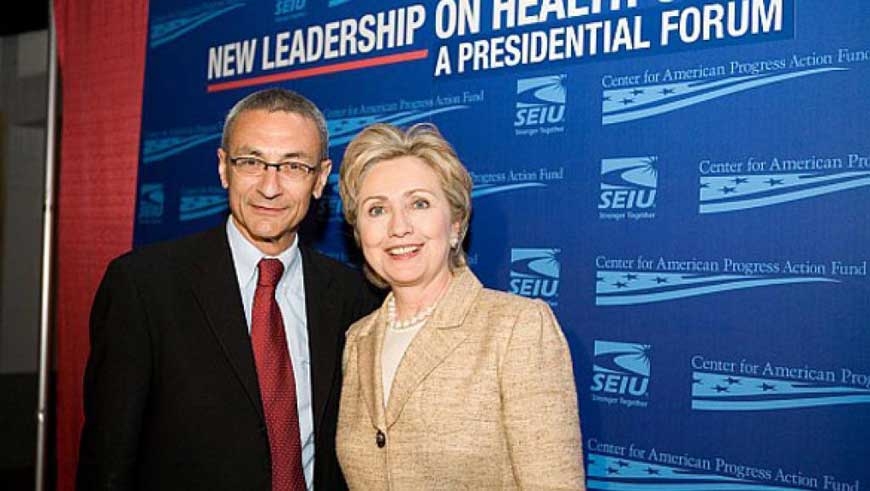
How did the Russians allegedly do it? They sent a variety of Phishing emails to various sources and hoped that people clicked on the same. For example John Podesta, the chairman of Hillary’s aide was sent this email. He forwarded it to an aide, who by mistake said that it was ok. As a result, the Russians had access to 60,000 of Podesta’s emails. Among those were mischievous emails, which showed Debbie Wasserman Schultz (ex-Chair of the DNC) and her aides trying to undermine the emerging candidature of Bernie Sanders. These were sent to Wikileaks who promptly published them in their website. Following this scandal, Debbie had to resign from her position as the DNC Chair. So who was she replaced by? Enter Donna Brazile, a Democratic strategist and a television commentator…
So after that, did the Democrats do an about turn and sort out their affairs? ‘Once bitten twice shy’ was probably a proverb that the Democrats either did not know or disliked. Donna Brazile was caught revealing questions that were going to be asked during the primaries debate to Clinton campaign officials. After getting caught, one would have expected Donna to be defensive and apologetic. But no, not Donna…. Maybe others…. But not Donna…. She gave out one of the coolest statements in recent times – “I am sorry to have been caught while cheating.” This, in essence, meant that the next time she does it, she will take all necessary precautions not to get caught ????
The charge that many Democrats and even some Republicans (mostly the anyone-but-Trump Republicans) are laying out is ‘How can a foreign country interfere in our elections?’ That statement can be slightly turned and reframed as ‘How can the U.S. interfere in any foreign elections?’ After all there are charges that the Obama government interfered in the Israeli elections of 2015 to oust Benjamin Netanyahu. The U.S. State department paid US $ 350,000 to an Israeli group named ‘OneVoice’ to support the NGO’s efforts to back Israeli-Palestinian peace settlement negotiations. However, they allegedly used it to build a voter database, train activists and hire a political consulting firm with ties to Obama’s campaign – all of which set the stage for an anti-Netanyahu campaign.
In one finding, the subcommittee, which investigated the issue, even said that OneVoice told the U.S. State Department’s top diplomat in Jerusalem of its plans in an email. But the official Consul General Michael Ratney claims to have never seen them. The email was deleted permanently and hence there was no trail left for the subcommittee to verify the claims. OneVoice allegedly also deleted the State Department’s logo from the list of “partners” on its website. It is true that the subcommittee which investigated the charges found that there was no evidence that the NGO used funds to influence Israeli elections. But questions still remain – is it true that OneVoice deleted the U.S. State Departent’s logo from its website? If so, why would they do it?
Were there any motives for Obama to have worked against Netanyahu? Yes, there were. The Obama-Netanyahu rivalry started in early 2009 when they clashed over Israeli settlements in the West Bank. Later during the 2012 elections, Netanyahu gave out a perception, through his close friendship with Mitt Romney, which went back to their working for a Boston investment firm in the 1970s and also through his close friendship with Pro-Romney Superpac donor Sheldon Adelson, that he backed Romney. He also criticised Obama publicly over the Iran nuclear deal in September of 2012, a few months before the U.S. elections. All these did not help the cause.
Of course, that is not all. The U.S. has meddled in the Maidan protests in Ukraine too. The Maidan Protests started in Kiev, Ukraine, in 2013. Victoria Nuland, the State Department’s top diplomat to Europe under the Obama regime, admitted that around U.S. $ 5 billion was poured in for assisting Ukrainians in building “democratic skills and institutions.” What were the beautiful democratic skills and institutions developed in Ukraine that required a whooping U.S. $ 5 billion? Sadly, Victoria Nuland throws no light on that. Later, in February of 2014, a leaked audio tape appeared on the net which showed the two diplomats Victoria Nuland and Ambassador Geoffrey Pyatt discussing who should lead the Ukrainian government and who should not. Hence it is clear that the U.S. had a role in the Maidan protests. “I think Yats (Arseniy P Yatsenyuk) is the guy who’s got the economic experience, the governing experience” says Victoria in the tape. What a stylish way of saying that!!!!
Two examples should suffice though one can write about a few more like the allegations against the Democratic Senator Edward ‘Ted’ Kennedy (youngest brother of John F Kennedy), who contacted the KGB leadership and asked for help in defeating the then U.S. President Ronald Reagan in the early 1980s. Let us assume that the present allegations against Russia are true. But what are the Russians alleged to have done? Have they bribed the voters and induced them to vote against Hillary Clinton? No, they have not. Of course, bribing the voters is a specialty unique only to India!!! So, have they manipulated the results by hacking the voter machines and tried to change the election outcome through bogus votes? No, they have not. What else have they done? They have hacked the DNC and revealed all the manipulations which went on behind closed doors in the Democratic Party. So what is the big fuss about…….
Disclaimer: Views expressed in this article are those of the author